Hacking, phishing, and incidents of identity thefts have become a regular phenomenon not only for PCs but also for Android mobile devices. Almost every day we hear about hackers and cyber criminals hacking apps using high-tech hacking tools that affect countless people globally by exposing them to privacy and security risks. In the month of May this year, more than 100 million LinkedIn passwords were hacked and sold by hackers. Besides this, American e-commerce and cloud computing company Amazon.com suffered a serious security breach in July this year when a hacker claimed to have leaked the login credentials of 80,000 Kindle users.
With so many advanced hacking tools used by powerful hackers, keeping oneself safe online seems to be an intimidating task. Malicious software created by cyber criminals constantly keeps an eye on our online activities via USB stick drives, Wi-Fi, and smartphones. Using social media apps may divulge your personal information to cyber criminals for malevolent activities. Thus, it becomes essential to monitor your social media accounts and integrated apps to ensure your personal data is not being used unnecessarily.
App Permission– Its Significance
Currently, smartphones have become the most preferred way of accessing the social media. All you need to do is install the social media app of your choice from Android Play Store. However, while installing an app from the Play Store, the app asks for your consent to view your location, contact list, browsing history, photos, and other vital information, known as ‘permissions’. You have the power to decide and manage which permission you want the social media app to access once you install it on your mobile device.
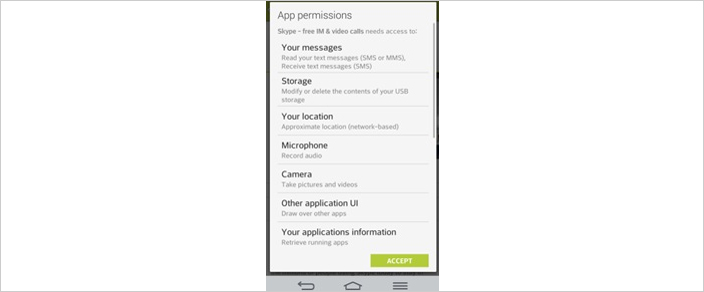
However, since a majority of app users are ignorant about the importance of controlling app permissions, they end up clicking the “Agree” button blindly, without thinking of the hazardous consequences of the app accessing their contact list or web camera. Some of the third-party apps that you integrate your social media account with may even end up selling your personal details without your knowledge. If you are not cautious enough, you may pave way for those third party apps to hack your phone easily and use your personal data. In order to secure your online presence, it becomes crucial to know how app permissions function so that you can keep your online data safe and secure. Thus, before downloading an app on your mobile device, you should go through the app permissions without fail. One such example mentioned below is for Skype:
Source: https://joyofandroid.com/how-to-get-complete-privacy-details-of-my-android-phone/
How to Check For App Permissions?
- While installing a social media app, if the app asks for too much superfluous permission, it is advisable not to download the app. For example, Facebook stores a lot of information about you; such as– your location, age, relationships, likes, dislikes, and so on. This significant assortment of data can be accessed by apps connected to your Facebook account, for example, Instagram, Twitter, Flickr, and game apps. Thus, it is necessary to control the access of such data.
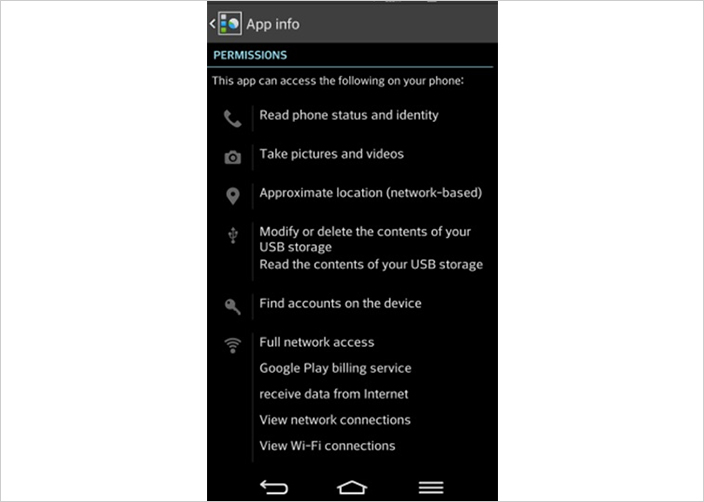
2. If you have already installed social media apps on your phone that are used by you frequently, uninstalling and reinstalling each and every app may not be practically possible. Therefore, it is advisable to view the app permissions of the already installed apps. All you need to do is go to your phone’s settings and tap on your phone’s App Manager to view the list of social media apps you have downloaded on your device. By tapping on a specific app, you can view its details along with the permissions tab. Click on the permission tab to view the list of information that the app can access. While doing so, if you feel that any specific app is gaining unnecessary access to your personal data, you should uninstall the app immediately.
Source: https://joyofandroid.com/how-to-get-complete-privacy-details-of-my-android-phone/
- In order to check your social media pages for privacy hazards and hazardous interconnections, it is highly recommended that you disable unnecessary app permissions by installing apps like MyPermission extension. This app allows you to keep or uninstall social media apps by monitoring your installed apps and checking the exact functions that have been permitted by you.
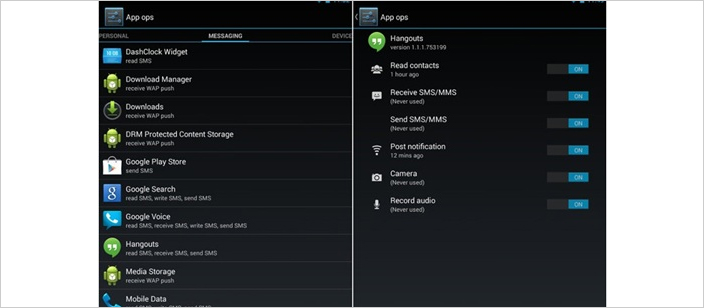
Besides this, there are apps like App Ops, Privacy Guard and XPrivacy that grant only those permissions that a specific app is authorized to use by blocking all unessential app permissions sent by certain apps to your smartphone that have nothing to do with the key function of the app.
It is very easy to use these apps. Go to your app list and tap any app to see the listed permissions the particular app can access and when it used the accessible permissions. Each permission granted by you has an ON and OFF on its right side. You can deactivate any unwanted permission you like. For example, you do not want Facebook to read and modify your contacts, tap Facebook and choose the OFF button for ‘Read and Modify Contacts’ tab.
Source: https://thehackernews.com/2015/06/android-permission-manager.html
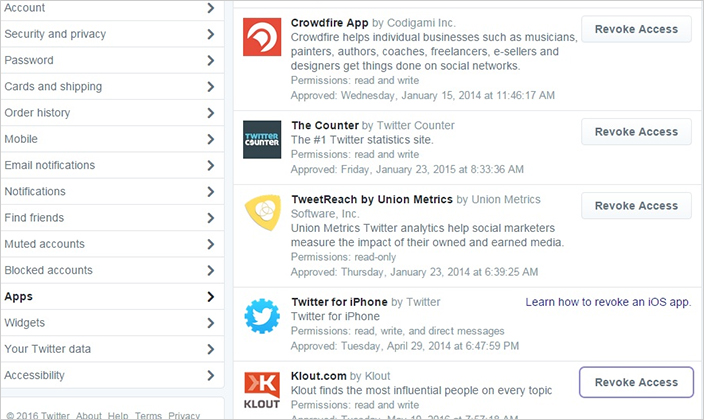
Another platform that you can also check for app permission is your Twitter account. All you have to do is go into your apps section and check the ones you have given access to. You can revoke the access based on the usage of app, as shown below:
How to Prevent Hackers from Hacking Your Personal Information?
Your smartphone stores a huge amount of data by linking your Google account to your Facebook, Twitter, LinkedIn, Pinterest, Foursquare, and Instagram accounts. Granting access to a suspicious app can spell disaster as a cyber-criminal can steal, tamper with, or even sell your personal data for spreading malware. If you want to secure yourself from cyber-attacks, you need to be ever-vigilant by taking certain precautions. The few guidelines on app permissions cited below will help our readers stay safe from getting hacked.
- It is advisable to lock the social media apps used frequently by you. There are many third-party apps available for locking your apps using a password that is difficult for hackers to guess. Ideally, you should pick an alphanumeric password which is a combination of upper and lower case with numbers. Alternatively, you may pick an unusual sentence that you can easily memorize.
- You should refrain from using the same password for different accounts. That said, even a strong password can be hacked by powerful hackers. The best way to keep hackers at bay is to enable a two-factor authentication on your social media accounts. The two-factor authentication system asks you to enter a secret code sent to your smartphone as and when you log in from a new device or location.
- At times you may integrate different apps such as WordPress or Instagram to your Facebook or Twitter account. However, make sure you remove all the integrated apps that are no longer used by you. This can be done through the settings page of your social media account.
- You should never reveal your username or passwords unless you are fully confident about the authenticity of the website. You should also avoid clicking on suspicious links sent to you via emails from unknown people. Phishers often pose as a trustworthy company or a reputable individual to dupe people into giving away their personal information. Since such tricks are difficult to identify, people easily become the victims of such Phishing scams.
By following the instructions mentioned above, you can secure your social media accounts as well as your phone from the fraudulent activities of hackers. Every smartphone user should take measures to secure their private information from illicit access of hackers. By performing a screening procedure of each and every permission prior to installing any app and integrating them with your social media account, you can prevent malicious apps from accessing your personal information unnecessarily.